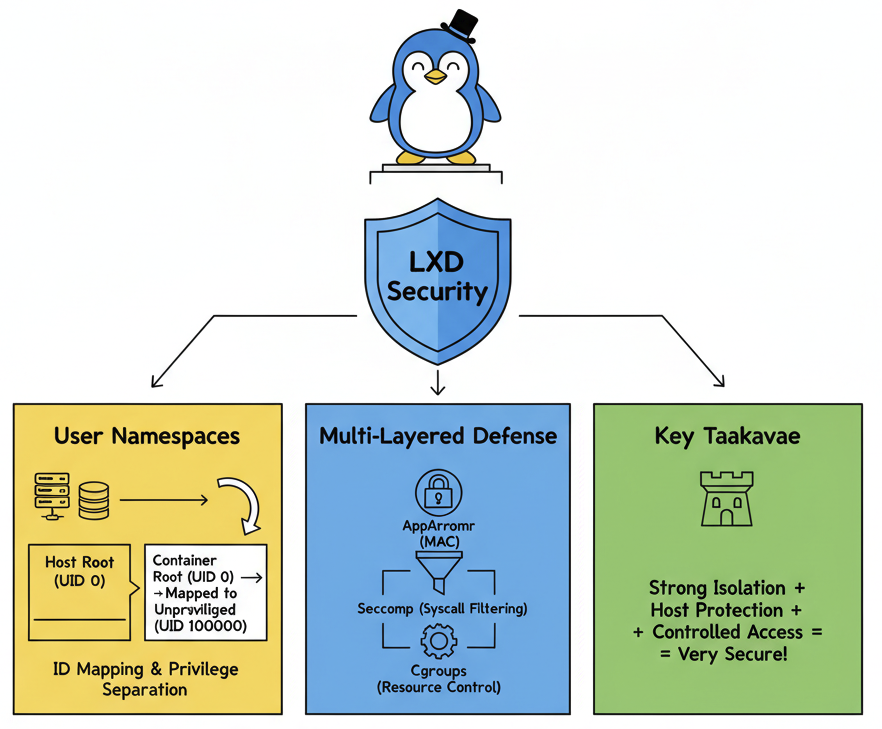
Key Takeaway: Very Secure by Default
Yes, LXD containers are very secure. LXD's design philosophy is "secure by default." It leverages a series of advanced Linux kernel features to achieve a strong level of isolation, close to that of virtual machines, while maintaining the lightweight performance of containers.
Unlike some earlier container technologies, LXD's unprivileged containers (the default setting) ensure that even a root user inside the container cannot pose a threat to the host machine.
The Core Defense: User Namespaces
This is the cornerstone of the LXD security model. A user namespace is a Linux kernel feature that allows a container to have its own independent set of user and group IDs (UIDs/GIDs) that are isolated from the host's IDs.
- ID Mapping: The root user (UID 0) inside the container is mapped to a high-numbered, unprivileged regular user on the host (e.g., UID 100000).
- Privilege Separation: This means that even if an attacker gains root access within the container, their access to the host's filesystem and resources is equivalent to that of a regular user, preventing any destructive actions.
Multi-Layered Defense: Other Security Mechanisms
In addition to user namespaces, LXD integrates several other Linux security features to build a defense-in-depth architecture:
AppArmor
LXD enables a separate AppArmor profile for each container by default. This is a Mandatory Access Control (MAC) system that restricts programs to a limited set of resources by defining rules for accessing files, network ports, and capabilities. Even if a process is compromised, AppArmor prevents it from performing actions outside its predefined scope.
Seccomp
The Seccomp mechanism allows for strict filtering of the system calls (syscalls) that processes within a container can make to the kernel. LXD defaults to filtering out a large number of dangerous and unnecessary syscalls, significantly reducing the kernel's attack surface.
Cgroups (Control Groups)
While primarily used for resource management (limiting CPU, memory, disk I/O), Cgroups also serve as a security tool. By preventing a single container from exhausting all system resources, it effectively defends against Denial of Service (DoS) attacks.
Conclusion: A Security Fortress for Modern Infrastructure
LXD doesn't just place processes in a container; it builds a secure "sandbox" through a carefully designed, multi-layered security model. It combines the most powerful isolation technologies in the Linux kernel to ensure:
- Strong Host Protection: Activities within a container can hardly affect the host or other containers.
- Clear Privilege Boundaries: The root user inside a container is no longer the system's super administrator.
- Controlled Resource Access: Access to files, the network, and system calls is strictly limited.
Therefore, for scenarios requiring strong isolation, high performance, and a full operating system environment, LXD is an exceptionally secure and reliable choice.